Computer networks are essential to modern corporate operations in the digital age. Every enterprise needs a dependable and secure computer system to perform efficiently, from IT companies to event venues, and retail stores to manufacturing sites. The fundamentals of computer networks, including their protocols, structures, and security methods, will be covered in this article. We’ll also provide helpful advice for businesses looking to safeguard their systems.
What Are Computer Networks, and Why Are They Important?
A computer system is a group of linked devices that may communicate with one another to share resources and data. Computers, servers, printers, and other peripherals may be among these gadgets. The network may consist of just two devices or it may span the entire world and link millions of units.
According to TechTarget, a computer system is a group of interconnected nodes or computing devices that exchange data and resources with each other
It is impossible to exaggerate the role that computer networks play in contemporary corporate operations. Employers may share information and work together on projects thanks to networks, which boosts output and efficiency. Networks also enable companies to centralize data backup and storage, lowering the risk of data loss. Networks also offer remote access to corporate resources, making work-from-home and remote work arrangements possible.
Types of Computer Network Architectures
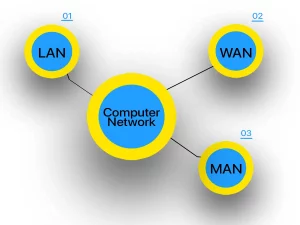
There are various sorts of computer system architectures, each with pros and cons. LAN, WAN, and MAN are the three most popular network architectures.
Local Area Network (LAN)
A local area network (LAN) refers to a network that covers a limited geographic area such as an office building or a school campus. LANs may be wired or wireless and are utilized to connect devices within a single location. With LANs, fast communication is possible, and they are comparatively straightforward to install and manage.
According to TechTarget, a local area network (LAN) is a group of computers and peripheral devices that share a common communications line or wireless link to a server within a distinct geographic area.
Wide Area Network (WAN)
A wide area network (WAN) is a type of system that spans over a vast geographic area, such as a country or even the world. WANs are commonly used to connect distant devices, including remote offices and data centers. They are connected through leased lines, satellites, and the internet. Despite their ability to connect devices across long distances, WANs offer slower communication speeds than LANs.
According to Spiceworks, it is possible to run a wide area network (WAN) solely with an in-house team and without the assistance of an external solution provider.
Metropolitan Area Network (MAN)
A Metropolitan Area Network (MAN) is a system that spans a larger geographical area than a LAN but is smaller than a WAN, such as a city or a county. MANs are typically used to connect devices within a specific metropolitan area and can be wired or wireless. MANs offer faster communication speeds than WANs but slower than LANs.
Cloudware states that MANs, similar to WANs, consist of interconnected LANs. However, because MANs cover smaller areas, they tend to be more efficient than WANs as data doesn’t need to travel long distances. Unlike WANs, MANs often combine the networks of multiple organizations and are not typically managed by a single organization.
Network Protocols
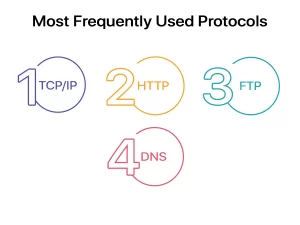
Network protocols are rules that determine how data is transmitted through a system. TCP/IP, HTTP, FTP, and DNS are the most frequently used protocols among several others.
Transmission Control Protocol/Internet Protocol (TCP/IP)
Transmission Control Protocol/Internet Protocol (TCP/IP) is the primary protocol used for communication over the Internet. TCP/IP divides data into packets and reassembles them at the receiving end. TCP/IP is a reliable protocol, ensuring that data is transmitted accurately and in the correct order.
Khan Academy states that TCP includes mechanisms to solve many of the problems that arise from packet-based messaging, such as lost packets, out-of-order packets, duplicate packets, and corrupted packets.
Hypertext Transfer Protocol (HTTP)
HTTP is a protocol that facilitates the transfer of data over the Internet. It governs the communication between web servers and browsers. However, HTTP is unsecured, which implies that third parties can intercept data transmitted via HTTP.
There is also a secure version of HTTP. The protocol is called HTTPS and is used for transmitting data over the Internet. HTTPS ensures that the communication between a user’s browser and a website is encrypted and secure, making it difficult for any third party to intercept or modify the data being transmitted. This is particularly important for sensitive information such as login credentials, personal data, and financial transactions, which require a high level of security. HTTPS is implemented by using SSL/TLS (Secure Sockets Layer/Transport Layer Security) encryption protocols.
TechTarget states that HTTPS plays a significant role in securing websites that handle or transfer sensitive data, including data handled by online banking services, email providers, online retailers, healthcare providers, and more. Simply put any website that requires login credentials or involves financial transactions should use HTTPS to ensure the security of users, transactions, and data.
File Transfer Protocol (FTP)
The File Transfer Protocol (FTP) is a protocol for exchanging files among networked devices. While uploading or downloading files to or from a web server, FTP is frequently used. Encryption can be used to protect FTP.
HOSTINGER TUTORIALS states that many people may have unknowingly used FTP before, especially when downloading files from a website. The process involves logging in with a username and password, accessing an FTP server through a specific port number, and then transferring files. While not all public FTP servers require signing in, some allow for anonymous access.
Domain Name System (DNS)
A protocol called Domain Name System (DNS) is used to convert domain names into IP addresses.
Instead of utilizing numerical IP addresses, DNS enables people to visit websites using familiar domain names. DNS operates by keeping a database of domain names and the IP addresses that go with them. The DNS system converts a domain name entered into a web browser into its matching IP address, enabling the browser to establish a connection with the appropriate web server.
Network Security

Modern corporate operations must take system security seriously. Businesses need to make sure their networks are secure in light of the rise in cyber threats in order to safeguard their data and daily operations. Malware, hacking, and data leaks are some of the most frequent security risks to computer systems.
Malware
Any software that is intended to damage computer systems or steal data is referred to as malware. Viruses, trojans, worms, and ransomware are just a few examples of the various types of malware. Infected emails, websites, and software downloads can all transmit malware. Once it has been deployed, malware can seriously harm a company’s system, leading to data loss, system malfunctions, and illegal access.
Hacking
Any unlawful effort to log into a computer system is referred to as hacking. Hackers can access a system using a number of techniques, such as password guessing, social engineering, or exploiting software flaws. Once inside, hackers have the ability to steal data, deploy malware, or harm the system.
Data Breaches
When private information is accessed, taken, or disclosed by unauthorized individuals, a data breach occurs. Human mistakes, viruses, and hackers are just a few of the causes of data breaches. For businesses, data breaches can lead to large financial losses, harm to their reputations, and legal penalties.
Network Security Measures
To mitigate the risks associated with cyber threats, companies must implement various security measures to protect their systems. Commonly used security measures include:
Firewalls
A firewall is a security mechanism that regulates incoming and outgoing network traffic. It can be either software or hardware-based and is capable of preventing unauthorized access to a network. Additionally, firewalls can detect and restrict malicious traffic, such as hacking attempts or malware.
Encryption
Encryption is the process of encoding data to prevent unauthorized access. Encryption can be used to secure data both in transit and at rest. Data encryption ensures that even if data is intercepted by a third party, they will not be able to read or access the data.
Employee Training
One of the most critical aspects of network security is employee training. Employees need to be aware of the risks of cyber threats and the steps they can take to protect the system. Regular training and awareness programs can help employees recognize and avoid common cyber threats, such as phishing emails or suspicious websites.
Continually Updating Your System
In order to keep a system secure, regular system updates are necessary. Bug fixes and security patches that address system vulnerabilities are frequently included in system updates. In order to defend their systems from the newest dangers, businesses should follow a frequent upgrade plan.
Monitoring of the network
Network monitoring refers to the practice of observing a system’s activities to identify and address security issues. By utilizing network monitoring software, system administrators can detect and alert potential security breaches by examining system traffic and identifying abnormal behavior. Adopting network monitoring can aid businesses in avoiding data loss or system damage by taking quick action to resolve security problems.
Computer networks are essential to contemporary corporate operations, to sum up.
The most popular network topologies are LAN, WAN, and MAN, each with pros and cons. Some of the most popular system protocols used to ease data exchange across networks are TCP/IP, HTTP, FTP, and DNS.
Businesses must put in place a number of security measures, such as firewalls, encryption, employee training, frequent system updates, and system monitoring, to safeguard their systems.
Businesses may safeguard their systems against cyber threats and maintain the continuity of their operations by adhering to these best practices.
It is crucial to keep in mind that system security is an ongoing activity rather than a one-time effort. To consistently defend their systems, businesses must follow best practices and stay abreast of the latest security trends. Investing in network security measures may appear to be an extra expense for organizations, but it is a little amount to pay compared to the harm to one’s finances and reputation caused by a security breach.
At ITAdOn, we specialize in offering complete IT assistance to companies of all sizes. A safe and dependable computer system that satisfies your business demands can be designed, implemented, and maintained with the assistance of our qualified experts. To find out more about our offerings and how we can assist you, get in touch with us today.
Check out our post on cable management if you’re interested in learning about how it can increase the system’s effectiveness and security. You can optimize your system infrastructure and lower the possibility of mishaps and downtime by using the useful advice and tactics you’ll find here.
Key Takeaways
- Computer networks are essential for modern business operations and allow devices to communicate with each other to share data and resources.
- LAN, WAN, and MAN are the most common system architectures, each with its advantages and disadvantages.
- TCP/IP, HTTP, FTP, and DNS are some of the most common system protocols used to facilitate data communication across networks.
- System security is critical to protect networks from cyber threats such as malware, hacking, and data breaches.
- Firewalls, encryption, employee training, regular system updates, and system monitoring are some of the most effective security measures businesses can take to protect their networks.